From Governance to Guardrails: The Board Must Shape Cyber, Not Just Fund Controls
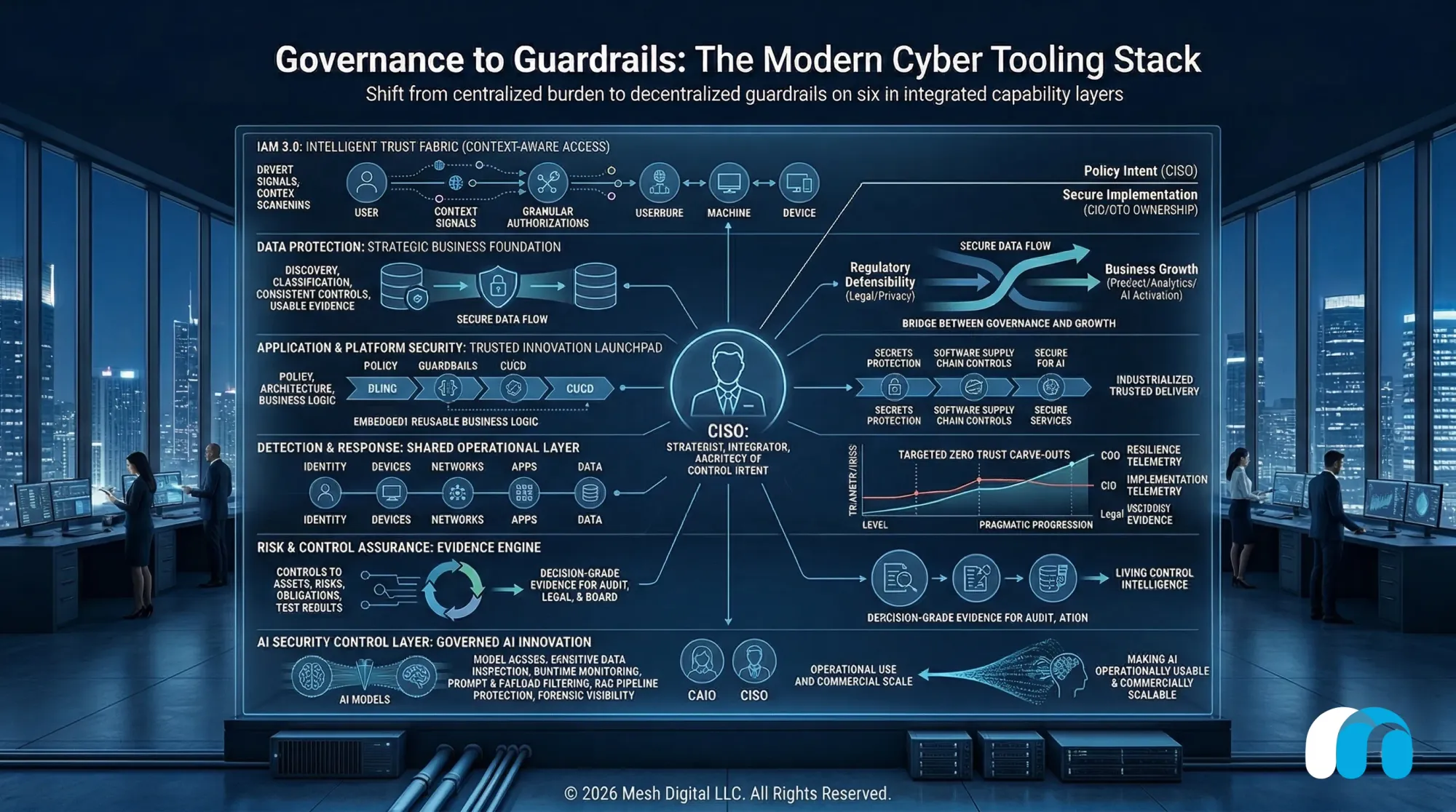
Modern cyber tooling should do more than reduce risk. When aligned to a reimagined cyber leadership model, it becomes the control fabric for trust, AI, resilience, and growth, helping regulated firms move faster, scale safer, and compete with more confidence.
In our recent article, Beyond the CISO: A New Blueprint for Cyber Leadership, we argued that the modern CISO has become a structural single point of failure. The problem is not that CISOs are underperforming. The problem is that many organizations still expect one executive to govern risk, resilience, privacy, assurance, engineering enablement, and regulatory defensibility all at once (Kleinberg & Tyler, 2026). That is not leadership design. It is executive compression.
This follow-on article tackles the obvious next question: if cyber responsibilities are redistributed across the enterprise, what role should modern cyber tooling play?
The answer is not “buy more tools.” In fact, the earlier article made the opposite point. Tool-centric security is a poor substitute for sound governance, clear decision rights, and capable operating models (Kleinberg & Tyler, 2026). But once those responsibilities are reimagined and properly aligned, tooling becomes essential. It stops being a patchwork of licenses and starts becoming the execution layer for a more mature cyber organization.
If your org feels like it’s sprinting in place, this is the shift your board needs to grasp today. A reimagined cyber model demands a reimagined cyber stack.
Tooling should follow decision rights
The principle is simple: tools should reinforce accountability, not blur it. NIST Cybersecurity Framework 2.0 is useful because it elevates governance and places cyber risk in the context of broader enterprise risk, from legal and privacy to reputational and operational exposure (National Institute of Standards and Technology [NIST], 2024). Just as important, it is not prescriptive. It provides a common language for prioritizing, communicating, and operationalizing cyber risk across the enterprise (NIST, 2024).
That is why the right tooling strategy is not one team owning every console. It is the enterprise sharing one control fabric. Different leaders need access to the controls, telemetry, automation, and evidence that support the risks they own. Not every executive needs another dashboard. Every executive does need visibility into the control system behind their accountability.
Enterprise Trust
Architecture
Identity
IAM 3.0: The Intelligent Fabric
Shifting from static gatekeeping to real-time trust mediation.
Identity is the enterprise control plane. By connecting workforce, customer, partner, and machine identities into a shared context layer, access is shaped by behavior and verified attributes—reducing friction while elevating security.
Data
Governance to Growth
Data as a strategic foundation, not just a compliance burden.
Tooling must bridge defensive protection with top-line growth. Trusted, connected data improves conversion, powers AI viability, and scales digital experiences.
Platform
The Launchpad
Closing the "English vs Geek" operating gap.
Translating business intent into reusable guardrails. By embedding compliance into the flow of work, the secure platform ensures the safest path is also the fastest path to production.
Zero Trust
Pragmatic Progression
A continuous evolution focused on high-risk carve-outs.
Not an overnight architectural flip. Implementing continuous verification, risk-based access, and resilience telemetry where boundaries are clear to build institutional muscle without halting the enterprise.
Assurance
The Evidence Engine
From static spreadsheets to living control intelligence.
Connecting policy directly to proof. Continuous mapping of controls to assets creates decision-grade evidence, making cyber risk legible to the board, legal, and regulators on demand.
AI Security
CriticalGoverned Architecture
Empowering the CAIO to industrialize AI safely.
Embedded controls for model access, prompt filtering, and RAG protection. AI security is the translation layer between ambition and scalable execution.
What the modern cyber tooling stack should actually do
In a reimagined cyber organization, the technology estate should behave less like a shopping cart and more like an operating system built across six capability layers.
Identity & Access Management
Identity must become the enterprise control plane, but not in the old IAM 2.0 model of monolithic directories, static roles, and brittle federation. In regulated enterprises, identity must operate as an intelligent fabric that connects workforce, customer, partner, and machine identities into a shared trust layer across applications, infrastructure, data, and increasingly AI systems. This is the practical promise of IAM 3.0. It shifts identity from static gatekeeping to real-time trust mediation, where access is shaped by context, behavior, verified attributes, and business policy, not passwords and stale role mappings alone (Kleinberg, 2026).
Across industries, the principle is the same: make access easier for the right actor, harder for the wrong one, and more provable for the enterprise. In healthcare, that can reduce clinician friction, speed onboarding, and support portable consent. In financial services, it can reduce onboarding abandonment, strengthen fraud resistance, and improve auditability. A mature identity layer should support phishing-resistant authentication, granular authorization, privileged access controls, continuous identity proofing, machine identity governance, and event-driven policy enforcement. Over time, leading firms will also adopt verifiable credentials, selective disclosure, and wallet-based identity where they create measurable value. This allows the CIO or CTO to own secure implementation in the first line while the CISO defines policy, control intent, and assurance expectations (Kleinberg, 2026).
Data Protection
Data protection must become more than a policy backbone. It must become a strategic business foundation. In many regulated enterprises, data is still treated as a compliance issue rather than an asset to govern, trust, and activate. That is too narrow. If legal, privacy, and compliance leaders are expected to own regulatory defensibility, they need more than static policies and annual reviews. They need tooling that can discover sensitive data, classify it, apply controls consistently, protect it across cloud and on-prem environments, and generate usable evidence. Otherwise, privacy ownership is just a title without machinery behind it.
But governance is only one side of the coin. The other is growth. A strong data foundation rooted in strategy, governance, and trust can improve the top line by making customer insight more reliable, personalization more precise, onboarding more intelligent, product decisions faster, and AI use cases more viable. The firms that outperform are not the ones with the most data. They are the ones whose data is trustworthy, connected, and governed well enough to scale. In healthcare, that can mean better patient engagement, cleaner care coordination, and stronger digital experiences. In financial services, it can mean sharper segmentation, lower onboarding friction, better fraud analytics, and more effective cross-sell and retention. Different industry, same principle: trusted data improves both control and conversion.
That is why modern data tooling should not be framed as only a defensive layer. It should bridge governance and growth. The right stack should help organizations understand what data they have, what it means, who can use it, under what conditions, and with what confidence. It should support lineage, policy enforcement, quality monitoring, entitlement-aware access, and evidentiary reporting, while enabling the business to activate data safely across analytics, digital channels, and AI systems. When designed well, data governance stops feeling like a brake pedal and starts acting like a performance system that protects the enterprise while helping it grow with more precision, speed, and trust.
Platform Security
Application and platform security must become more than a secure paved road. It must become the trusted foundation for building products, services, and innovation. That is especially true in an AI era, where the challenge is not just writing code faster, but translating business intent into reliable digital execution without losing control, quality, or trust. Too many organizations still operate inside an “English versus Geek” gap, where translation failures between business and engineering slow delivery, weaken adoption, and create costly rework. The platform layer should close that gap by turning policy, architecture, and business logic into reusable guardrails that support speed rather than resist it (Kleinberg, 2025b).
This is where secure platforms become commercially important. A strong application and platform stack does not just reduce risk. It shortens the distance between an idea and a production-grade capability. It gives product, engineering, data, and control teams a shared operating surface where secure patterns are prebuilt, tested, and repeatable. That includes secrets protection, code integrity, software supply chain controls, automated policy enforcement in CI/CD, cryptographic services, and reusable AI services such as secure model access, governed data pipelines, prompt controls, traceability, and human override patterns. In that sense, the platform is not just defensive. It is a launchpad.
The winners will not be the firms that generate more code or more pilots. They will be the ones that industrialize trusted delivery. They create environments where the safest path is also the fastest, where compliance is embedded into the flow of work, and where AI can move from experiment to capability without reinvention in every team. If the platform does not help move P&L, customer value, resilience, or managed risk, it is just technical theater. When designed well, it carries more of the enterprise’s security, trust, and execution logic by default, so the CISO no longer has to referee every engineering decision (Kleinberg, 2025a).
Zero Trust
Detection and response must become a shared operational layer, and it is worth being honest: for many firms with inherited entitlements, legacy applications, broad network access, and too many standing privileges, a full move to Zero Trust can feel nearly impossible. That reaction is understandable. Most organizations did not design for continuous verification, context-aware access, or least-privilege enforcement from the start. Their access model accumulated over time in service of speed, convenience, or acquisition-led integration. So the goal is not to re-architect every user, workload, and dependency overnight. The better path is pragmatic. Start with carve-outs where risk is meaningful, boundaries are clearer, and the operating model can absorb change. Done well, those carve-outs become proof points that build confidence, reduce blast radius, and create the muscle to scale further.
That is why Zero Trust should be understood less as a product and more as a progression. CISA’s Zero Trust Maturity Model emphasizes continuous verification, strong visibility, and integrated monitoring across identity, devices, networks, applications, and data. Thales makes a similar point: authentication and authorization should move closer to the resource, policies should become more granular, and identity, device, and service context should shape access in real time rather than relying on the assumption that anything inside the perimeter is safe. In practice, that means modern tooling should support strong multifactor authentication, risk-based access management, step-up authentication, tighter control of non-person entities, and encryption and key management across hybrid environments (Cybersecurity and Infrastructure Security Agency [CISA], 2023; Thales Trusted Cyber Technologies, n.d.).
In a reimagined organization, these capabilities should not sit in a black box for security analysts alone. The COO needs resilience telemetry. The CIO needs implementation telemetry. Legal needs incident evidence. The CISO needs cross-domain threat context. Just as important, business and technology leaders need to see that Zero Trust can improve control without halting the enterprise. That is why the best tooling strategies combine integrated detection, orchestration, and response with targeted Zero Trust enforcement where the organization is most ready to move. Not every access path has to change on day one. But firms that begin with the right carve-outs, supported by modern identity, access, encryption, and policy tooling, can make meaningful progress toward a more durable Zero Trust Architecture.
Assurance Engine
Risk and control assurance must become an evidence engine. One of cyber’s biggest failure modes is the gap between what leaders believe is controlled and what the environment can actually prove. The CRO cannot own cyber risk appetite if control effectiveness is still measured through spreadsheets and anecdote. The modern stack should continuously map controls to assets, risks, obligations, and test results. It should make evidence portable, timely, and decision-grade. That is how cyber becomes legible to finance, audit, legal, and the board.
This matters even more in regulated sectors like banking, financial services and insurance (BFSI) and healthcare, where the burden is rarely just to have controls. It is to prove, on demand, that those controls are operating as intended across complex environments, third parties, and shifting obligations. In banking, wealth, insurance, and payments, that evidence supports cyber oversight, model risk conversations, fraud controls, resilience expectations, supervisory scrutiny, and board confidence. In healthcare, it helps leaders navigate privacy, patient safety, clinical operations, medical device exposure, business associate risk, and the reality that digital experience failures can quickly become trust failures. Different sectors, same need: leaders need to know whether the control environment is truly working, not merely documented.
That is why assurance tooling is more than an audit convenience. It is the mechanism that connects policy to proof. When designed well, it helps financial institutions move from static compliance narratives to living control intelligence, and helps healthcare organizations move from fragmented oversight to more defensible, enterprise-wide trust. In both industries, stronger assurance reduces surprises and improves decision quality by giving executives, regulators, auditors, and operators a more current and credible view of where risk is being managed, where it is drifting, and where intervention is needed.
AI Security
AI security now deserves its own control layer, but the more important point is why. AI pilots are over. The Agentic Era demands more. In too many organizations, AI is still treated as a side project, an experimental sandbox, or a future compliance issue to sort out later. That is already outdated. NIST notes that cybersecurity and privacy considerations are increasingly relevant to the design, deployment, evaluation, and use of AI systems (NIST, 2024). In practical terms, AI can no longer be separated from the enterprise operating model. If it is becoming part of how products are built, services are delivered, workflows are automated, and decisions are supported, then it also has to become part of how control, trust, and accountability are designed.
This is where alignment with the CAIO becomes critical. As Kleinberg and Tyler (2026) argued in the earlier article, the rise of AI is creating a distinct executive mandate around AI strategy, enablement, governance, and value realization. But the CAIO cannot industrialize AI on aspiration alone. The function needs a control environment strong enough to let the business move. That includes tooling for model access control, sensitive data inspection, runtime monitoring, prompt and payload filtering, RAG pipeline protection, policy enforcement, and forensic visibility into how AI systems interact with enterprise data. Without that foundation, the organization tends to oscillate between reckless experimentation and institutional paralysis.
Firms that get this right unlock far more than safer AI. They create conditions for margin expansion because governed AI can automate more work with less rework, lower exception handling, and fewer downstream control failures. They accelerate innovation because product, operations, risk, and data teams no longer have to rebuild trust mechanisms for every new use case. They create competitive differentiation because they can move promising AI capabilities from pilot to production with more confidence, speed, and credibility than peers still trapped in fragmented tooling, vague policies, and improvised oversight. In other words, AI security is not just about preventing harm. It is about making AI operationally usable and commercially scalable.
Again, that matters across regulated sectors. In financial services, this control layer can support AI in customer onboarding, fraud operations, service workflows, and advisor or employee enablement without losing sight of model behavior, data exposure, or supervisory defensibility. In healthcare, it can support AI-enabled administrative automation, patient engagement, clinical support functions, and digital experience improvements while preserving privacy, trust, and human accountability. Different use cases, same pattern: once AI becomes part of the business model, trust architecture becomes part of the growth architecture.
Seen this way, AI security is not a bolt-on restraint. It is the translation layer between ambition and execution. It gives the CAIO a practical way to work with the CISO, CIO, CTO, legal, risk, and data leaders to turn AI from scattered experiments into governed enterprise capability. And for firms that can do that well, the payoff is not merely cleaner control. It is a stronger platform for innovation, sharper operating leverage, and a more durable edge in markets where trust increasingly determines who gets to scale first.
What changes for the CISO
None of this diminishes the CISO. It clarifies the role.
As Kleinberg and Tyler (2026) argued in Beyond the CISO: A New Blueprint for Cyber Leadership, cyber is no longer meant to sit as one executive’s catch-all burden. The CISO remains the strategist, the integrator, and the architect of control intent. But accountable ownership now sits more explicitly across the broader leadership team.
That matters here because modern cyber tooling should follow that same model. Identity, data, platform, resilience, assurance, and AI controls should not collapse back into one office simply because they live in software. The CISO helps bring those layers together into one coherent doctrine, while adjacent leaders own the parts of execution, risk, resilience, legal defensibility, and AI enablement assigned to them.
Put simply, the CISO should no longer be the universal sink for every unresolved cyber issue. The office becomes smaller, sharper, and more architectural, with a stronger focus on strategy, assurance, incident command, and executive alignment. The platforms then make that leadership model scalable.
The board-level implication
Boards should resist two temptations.
The first is to treat cyber tooling as a proxy for cyber maturity. It is not. The second is to underinvest in tooling because “this is really an operating model problem.” That is also wrong.
The better view is this: governance determines accountability, and tooling determines whether that accountability can function at scale.
That is the real so what. If boards and executive teams redesign cyber leadership but leave the control stack fragmented, they have not solved the problem. They have simply renamed it. The result will still show up in slower delivery, weaker resilience, AI hesitation, duplicated controls, and mounting execution drag.
The urgency is practical. AI adoption is accelerating. Regulatory scrutiny is not easing. Attack surfaces are still expanding. In regulated industries, the cost of incoherence now shows up not only in security incidents, but in stalled transformation, slower revenue activation, and reduced strategic agility.
The call to action is clear: align the cyber leadership model, rationalize the control stack, and start where the business can prove value quickly. Here is your 90-Day Plan:
- Act: Pick the carve-outs and define the ownership model.
- Measure: Rationalize the control stack against actual P&L and risk metrics.
- Go: Modernize the tooling layers that matter most using Strategy-in-Motion PODs™
The firms that move now will build a stronger platform for trust, speed, and growth. The ones that wait will keep paying for yesterday’s operating model with tomorrow’s constraints.
References
Cybersecurity and Infrastructure Security Agency. (2023, April 11). Zero trust maturity model. https://www.cisa.gov/resources-tools/resources/zero-trust-maturity-model
Kleinberg, M. D. (2025a, November 1). Engineering alone won’t save you. It’s time for a commercial operating model. Mesh Digital LLC Insights. https://insights.meshdigital.io/engineering-alone-wont-save-you-its-time-for-a-commercial-operating-model/
Kleinberg, M. D. (2025b, November 22). Translating English to Geek (and back): How AI can finally fix user acceptance testing. Mesh Digital LLC Insights. https://insights.meshdigital.io/translating-english-to-geek-and-back-how-ai-can-finally-fix-user-acceptance-testing/
Kleinberg, M. D. (2026, January 4). The death of the IAM monolith: Dismantling the identity tax in financial services and healthcare. Mesh Digital LLC Insights. https://insights.meshdigital.io/the-death-of-the-iam-monolith-dismantling-the-identity-tax-in-financial-services-and-healthcare/
Kleinberg, M. D., & Tyler, M. (2026, March 29). Beyond the CISO… a new blueprint for cyber leadership. Mesh Digital LLC Insights. https://insights.meshdigital.io/beyond-the-ciso-a-new-blueprint-for-cyber-leadership/
National Institute of Standards and Technology. (2024). The NIST Cybersecurity Framework (CSF) 2.0 (NIST CSWP 29). https://doi.org/10.6028/NIST.CSWP.29
Thales Trusted Cyber Technologies. (n.d.). Zero trust. https://www.thalestct.com/zero-trust/

